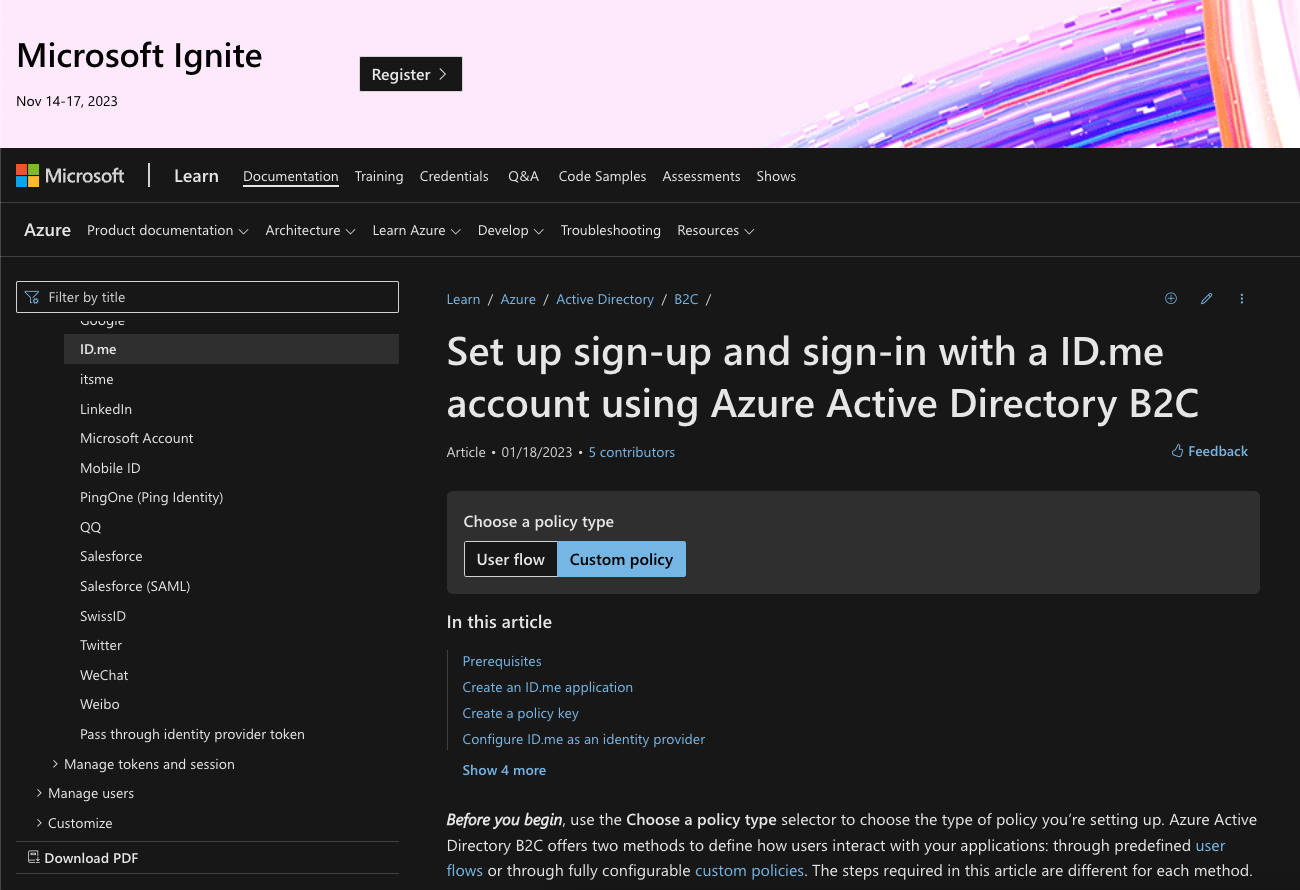
Set up sign-up and sign-in with a ID.me account using Azure Active Directory B2C
Prerequisites
Create an ID.me application
To enable sign-in for users with an ID.me account in Azure Active Directory B2C (Azure AD B2C), you need to create an application in ID.me Developer Resources for API & SDK. For more information, see OAuth Integration Guide. If you don’t already have an ID.me developer account, you can sign up at https://developers.id.me/registration/new.
- Sign in to the ID.me Developer Resources for API & SDK with your ID.me account credentials.
- Select View My Applications, and select Continue.
- Select Create new
- Enter a Name, and Display Name.
- In the Redirect URI, enter https://your-tenant-name.b2clogin.com/your-tenant-name.onmicrosoft.com/oauth2/authresp. If you use a custom domain, enter https://your-domain-name/your-tenant-name.onmicrosoft.com/oauth2/authresp. Replace your-tenant-name with the name of your tenant, and your-domain-name with your custom domain.
- Click Continue.
- Copy the values of Client ID and Client Secret. You need both to add the identity provider to your tenant.
Create a policy key
You need to store the client secret that you previously recorded in your Azure AD B2C tenant.
- Sign in to the Azure portal.
- Make sure you’re using the directory that contains your Azure AD B2C tenant. Select the Directories + subscriptions icon in the portal toolbar.
- On the Portal settings | Directories + subscriptions page, find your Azure AD B2C directory in the Directory name list, and then select Switch.
- Choose All services in the top-left corner of the Azure portal, and then search for and select Azure AD B2C.
- On the Overview page, select Identity Experience Framework.
- Select Policy Keys and then select Add.
- For Options, choose Manual.
- Enter a Name for the policy key. For example, IdMeSecret. The prefix *B2C_1A_** is added automatically to the name of your key.
- In Secret, enter your client secret that you previously recorded.
- For Key usage, select Signature.
- Click Create.
Configure ID.me as an identity provider
To enable users to sign in using an ID.me account, you need to define the account as a claims provider that Azure AD B2C can communicate with through an endpoint. The endpoint provides a set of claims that are used by Azure AD B2C to verify that a specific user has authenticated.
You can define a ID.me account as a claims provider by adding it to the ClaimsProviders element in the extension file of your policy.
- Open the TrustFrameworkExtensions.xml.
- Find the ClaimsProviders element. If it does not exist, add it under the root element.
- Add a new ClaimsProvider as follows:
<ClaimsProvider>
<Domain>id.me</Domain>
<DisplayName>ID.me</DisplayName>
<TechnicalProfiles>
<TechnicalProfile Id="IdMe-OAuth2">
<DisplayName>IdMe</DisplayName>
<Protocol Name="OAuth2" />
<Metadata>
<Item Key="ProviderName">api.id.me</Item>
<Item Key="authorization_endpoint">https://api.id.me/oauth/authorize</Item>
<Item Key="AccessTokenEndpoint">https://api.id.me/oauth/token</Item>
<Item Key="ClaimsEndpoint">https://api.id.me/api/public/v2/attributes.json</Item>
<Item Key="HttpBinding">POST</Item>
<Item Key="scope">openid alumni</Item>
<Item Key="UsePolicyInRedirectUri">0</Item>
<!-- Update the Client ID below to the Application ID -->
<Item Key="client_id">Your ID.me application ID</Item>
</Metadata>
<CryptographicKeys>
<Key Id="client_secret" StorageReferenceId="B2C_1A_IdMeSecret"/>
</CryptographicKeys>
<OutputClaims>
<OutputClaim ClaimTypeReferenceId="issuerUserId" PartnerClaimType="uuid" />
<OutputClaim ClaimTypeReferenceId="givenName" PartnerClaimType="fname" />
<OutputClaim ClaimTypeReferenceId="surname" PartnerClaimType="lname" />
<OutputClaim ClaimTypeReferenceId="displayName" PartnerClaimType="name" />
<OutputClaim ClaimTypeReferenceId="email" PartnerClaimType="email" />
<OutputClaim ClaimTypeReferenceId="identityProvider" DefaultValue="me.id.com" AlwaysUseDefaultValue="true" />
<OutputClaim ClaimTypeReferenceId="authenticationSource" DefaultValue="socialIdpAuthentication" AlwaysUseDefaultValue="true" />
</OutputClaims>
<OutputClaimsTransformations>
<OutputClaimsTransformation ReferenceId="CreateRandomUPNUserName" />
<OutputClaimsTransformation ReferenceId="CreateUserPrincipalName" />
<OutputClaimsTransformation ReferenceId="CreateAlternativeSecurityId" />
<OutputClaimsTransformation ReferenceId="CreateDisplayNameFromFirstNameAndLastName" />
</OutputClaimsTransformations>
<UseTechnicalProfileForSessionManagement ReferenceId="SM-SocialLogin" />
</TechnicalProfile>
</TechnicalProfiles>
</ClaimsProvider>
- Set client_id to the application ID from the application registration.
- Save the file.
Add the claims transformations
Next, you need a claims transformation to create the displayName claim. Add the following claims transformation to the ClaimsTransformations element within BuildingBlocks
<BuildingBlocks>
<ClaimsTransformations>
<ClaimsTransformation Id="CreateDisplayNameFromFirstNameAndLastName" TransformationMethod="FormatStringMultipleClaims">
<InputClaims>
<InputClaim ClaimTypeReferenceId="givenName" TransformationClaimType="inputClaim1" />
<InputClaim ClaimTypeReferenceId="surName" TransformationClaimType="inputClaim2" />
</InputClaims>
<InputParameters>
<InputParameter Id="stringFormat" DataType="string" Value="{0} {1}" />
</InputParameters>
<OutputClaims>
<OutputClaim ClaimTypeReferenceId="displayName" TransformationClaimType="outputClaim" />
</OutputClaims>
</ClaimsTransformation>
</ClaimsTransformations>
</BuildingBlocks>
<OrchestrationStep Order="1" Type="CombinedSignInAndSignUp" ContentDefinitionReferenceId="api.signuporsignin">
<ClaimsProviderSelections>
<ClaimsProviderSelection TargetClaimsExchangeId="IdMeExchange" />
</ClaimsProviderSelections>
</OrchestrationStep>
<OrchestrationStep Order="2" Type="ClaimsExchange">
<ClaimsExchanges>
<ClaimsExchange Id="IdMeExchange" TechnicalProfileReferenceId="IdMe-OAuth2" />
</ClaimsExchanges>
</OrchestrationStep>
Test your custom policy
- Select your relying party policy, for example B2C_1A_signup_signin.
- For Application, select a web application that you previously registered. The Reply URL should show https://jwt.ms.
- Select the Run now button.
- From the sign-up or sign-in page, select ID.me to sign in with ID.me account.
If the sign-in process is successful, your browser is redirected to https://jwt.ms, which displays the contents of the token returned by Azure AD B2C.
Useful Links

OpenID Connect
Set up sign-up and sign-in with a ID.me account using Azure Active Directory B2C (Azure AD B2C) using OIDC.

SAML
Set up sign-up and sign-in with a ID.me account using Azure Active Directory B2C (Azure AD B2C) using SAML.